Author: Jason Kellington
Featured
-

Measuring the impact of our AI investments in IT at Microsoft
As an IT organization, we need to understand which of our AI investments are creating…
-

Transforming facility operations at Microsoft with AI maps
Indoor building maps matter the moment accurate location data become important to solving an issue…
-

Deploying Microsoft Baseline Security Mode at Microsoft: Our virtuous learning cycle
The enterprise security frontier isn’t just evolving. It’s accelerating beyond the limits of traditional security…
All posts by Jason Kellington
-

Visualizing success: Steering your AI deployment with a strategy council
The pace of change when it comes to AI’s impact on business today is astounding.…
-

Powering the technical veracity of AI at Microsoft with a Center of Excellence
When we launched our AI Center of Excellence (CoE) in 2023, we had a straightforward…
-
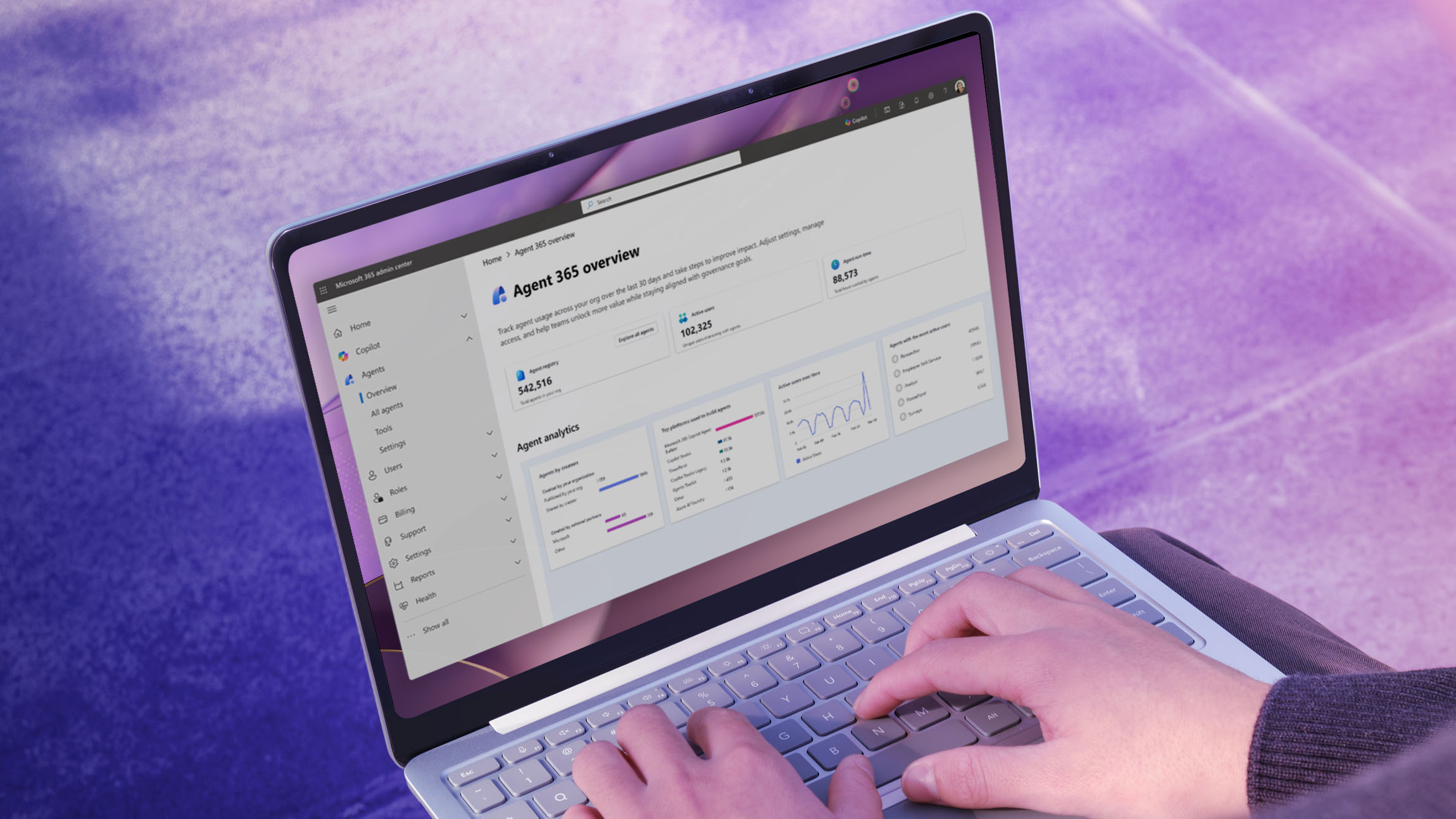
Shaping AI management at Microsoft with Agent 365 and Copilot controls
AI is moving fast at Microsoft. Every month, we’re discovering new ways that our employees…
-

Powering the new age of AI-led engineering in IT at Microsoft
When generative AI burst into the mainstream, it landed in our IT engineering organization like…
-

Protecting anonymity at scale: How we built cloud-first hidden membership groups at Microsoft
Some Microsoft employee groups can’t afford to be visible. For years, we supported email‑based communities…
-

Read our seven tips for shifting to a ‘cloud native’ device management strategy
At Microsoft, we manage a large, diverse device estate, with more than 1 million devices…
-
Protecting AI conversations at Microsoft with Model Context Protocol security and governance
When we gave our Microsoft 365 Copilot agents a simple way to connect to tools…
-

Accelerating our cultural transformation at Microsoft with Viva and AI
We’re learning a lot from integrating AI into our use of Microsoft Viva here at…
-

Supercharging our enterprise with Windows 11 and AI PCs
AI is no longer a buzzword—it’s the engine driving a new era of productivity, security,…
-
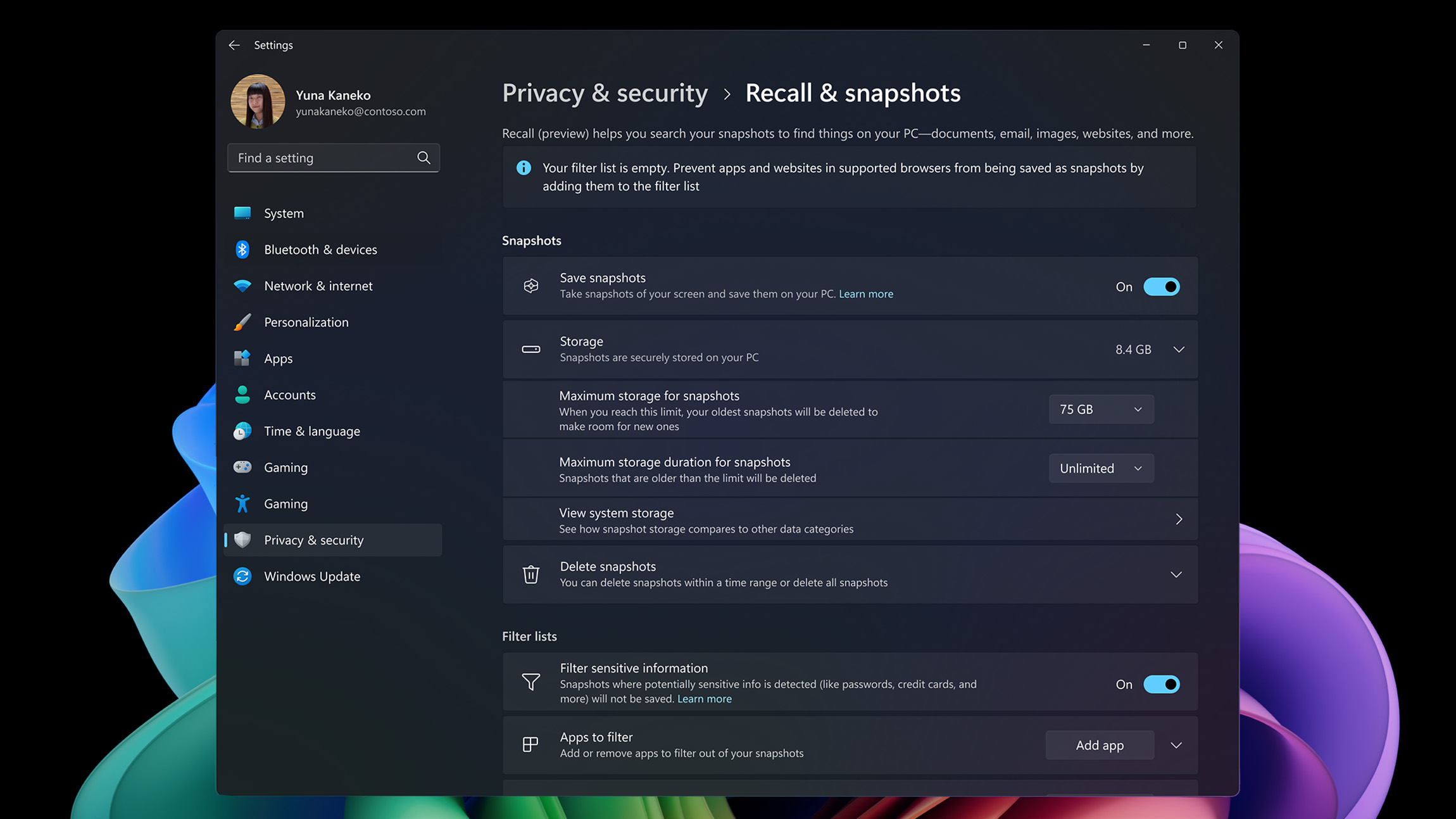
Accelerating workplace productivity at Microsoft with Windows Recall
Have you ever struggled to find an important document or photo? Forgotten which app a…
-

Hardening our digital defenses with Microsoft Baseline Security Mode
Security isn’t just a feature—it’s a foundation. As threats grow more varied, widespread, and sophisticated,…
-

Transforming security and compliance at Microsoft with Windows Hotpatch
Security updates are essential, and every security admin knows that when it comes to applying…
