Recently we have seen an emerging trend among malware distributors – Bitcoin miners being integrated into installers of game repacks.
This type of system hijacking is just one of the many ways to exploit a user by utilizing their system’s computing resources to earn more cash. Malware is easily bundled with game installers that are then uploaded and shared with unsuspecting users using torrent download sites. Once a machine is infected, a downloaded Bitcoin miner silently carries out mining operations without the user’s consent.
We have seen this technique used by Trojan:Win32/Maener.A. This threat is dropped by TrojanDropper:Win32/Maener.A as a bundle with some games. Some of the torrent files names we have seen bundled with this threat are:
- Tom Clancy’s Ghost Recon.Future Soldier.Deluxe Edition.v 1.7 + 3 DLC.(Новый Диск).(2012).Repack
- Don’t Starve.(2013) [Decepticon] RePack
- Kings Bounty Dark Side by xatab
- Sniper_Elite_III_8_DLC_RePack_MAXAGENT
- TROPICO_5
- Ghost_Recon_Future_Soldier_v1.8_Repack
- Trials.Fusion.RePack.R.G.Freedom
- King’s Bounty Dark Side.(2014) [Decepticon] RePack
- Watch Dogs.(2014) [Decepticon] RePack
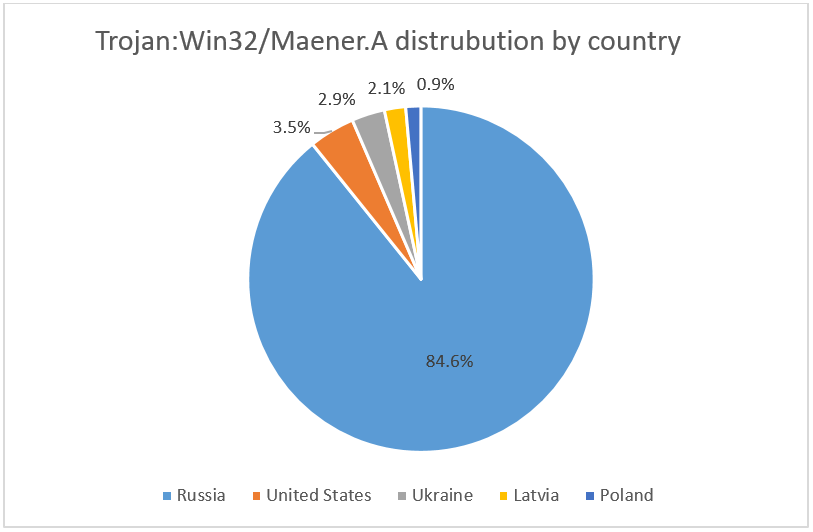
These files can be easily acquired by anyone who downloads games from a torrent website. The games are repacked to further lure gamers to download the compressed files for free. The installer that we detect as TrojanDropper:Win32/Maener.A is available in Russian and English languages only. It seems to be primarily affecting Russian users, as shown by its infection telemetry.
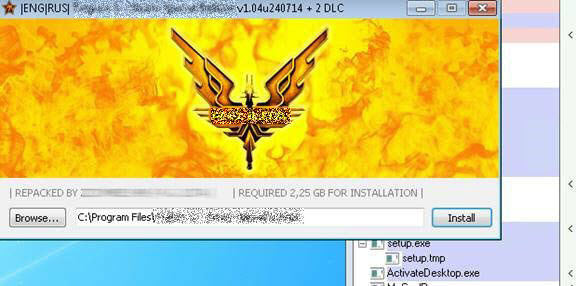
An example of the game installer execution is depicted in Figure 2. When the installer application (setup.exe) is run, Trojan:Win32/Maener.A also executes in the background and downloads its Bitcoin mining components.
Trojan:Win32/Maener.A can be found running under the filename ActivateDesktop.exe. It uses this reputable file name in order to hide its true identity. When run, it connects to a remote server, eventually downloading a Bitcoin miner and installing it on the system.
The Bitcoin miner is installed as connost.exe and can be launched with the command prompt:
- Connost.exe -a m7 -o stratum+tcp://<removed>:port -u <user> -p <password>.
We have also seen this miner use the file names minerd.exe, svchost.exe and winhost.exe.
Trojan:Win32/Maener.A also adds the following registry entry to enable its automatic execution at every system startup:
- HKCUSoftwareMicrosoftCurrentVersionRun
GoogleUpdate_CF4A51A46014ACCDC56E3A64BAC64B76 = c:Trash-100ActivateDesktop.exe
To help stay protected, we recommend you to install an up-to-date, real-time protection security product such as Microsoft Security Essentials, or Windows Defender for Windows 8.1. And, most importantly, only download from legitimate and reputable sources.
Donna Sibangan
SHA1s
3e4c9449d89c29f4e10186cc1b073d45d33c5f83
ebcd1aa912dfe00cb2d41de7097dedd1f9ab9127
f6b98be4091d108c6195ac543bf949ba3cffb8bf
Talk to us
Questions, concerns, or insights on this story? Join discussions at the Microsoft community and Windows Defender Security Intelligence.
Follow us on Twitter @WDSecurity and Facebook Windows Defender Security Intelligence.







