

Cyberattacker techniques, tools, and infrastructure
Cyberattackers constantly evolve their techniques, tools, and infrastructure to launch increasingly complex attacks. Learn about the latest tactics and how to detect, disrupt, and defend against them.
Refine results
Topic
Products and services
Publish date
-
 Our analysis of a targeted attack that used a language-specific word processor shows why it’s important to understand and protect against small-scale and localized attacks as well as broad-scale malware campaigns.
Our analysis of a targeted attack that used a language-specific word processor shows why it’s important to understand and protect against small-scale and localized attacks as well as broad-scale malware campaigns. -

Windows Defender Antivirus can now run in a sandbox
Windows Defender Antivirus has hit a new milestone: the built-in antivirus capabilities on Windows can now run within a sandbox. -

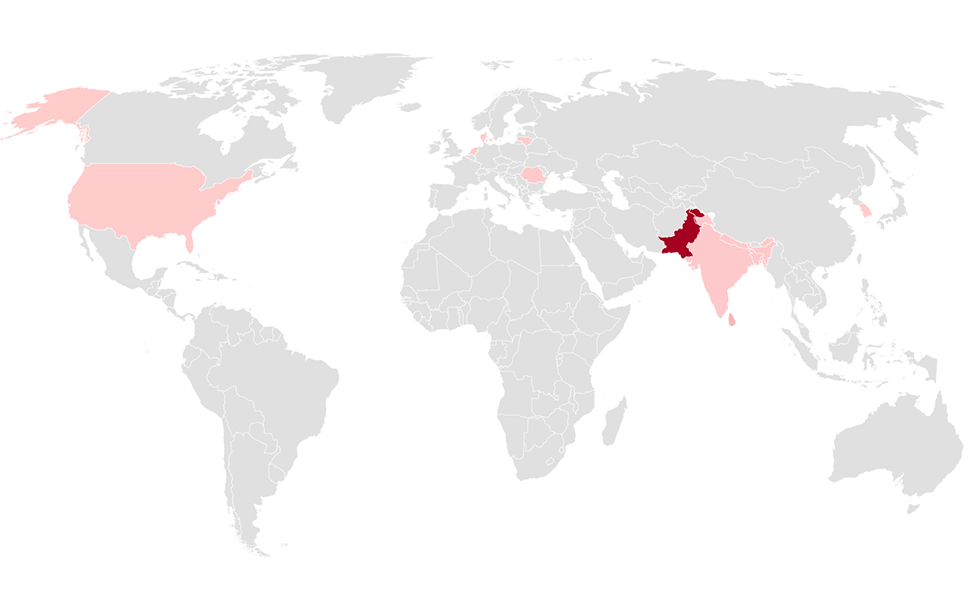
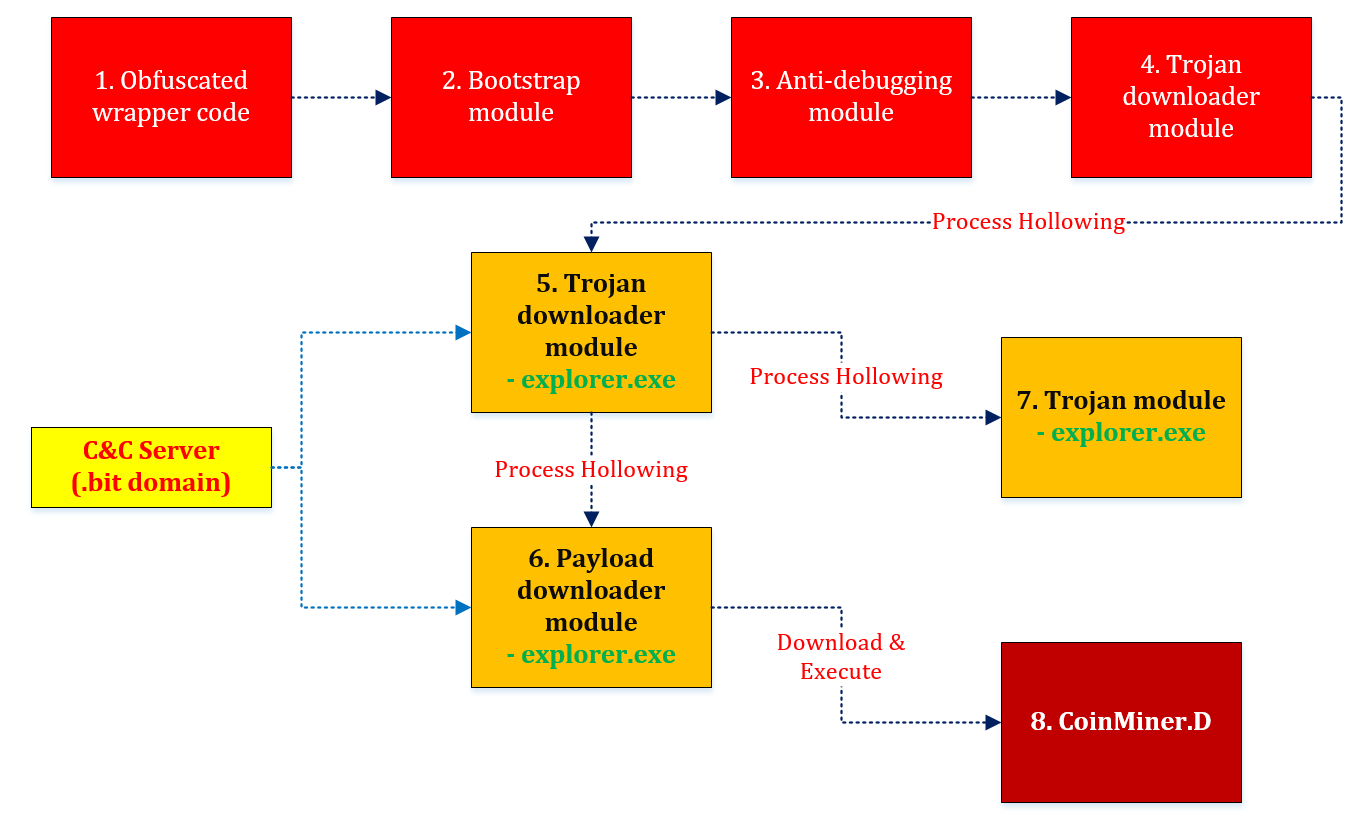
Small businesses targeted by highly localized Ursnif campaign
In social engineering attacks, is less really more? A new malware campaign puts that to the test by targeting home users and small businesses in specific US cities. -
Hawkeye Keylogger – Reborn v8: An in-depth campaign analysis
Hawkeye Keylogger is an info-stealing malware that’s being sold as malware-as-a-service. -
Teaming up in the war on tech support scams
Beyond customer education, the scale and complexity of tech support scams require cooperation and broad partnerships across the industry. -
Hunting down Dofoil with Windows Defender ATP
Dofoil is a sophisticated threat that attempted to install coin miner malware on hundreds of thousands of computers in March, 2018. -
Poisoned peer-to-peer app kicked off Dofoil coin miner outbreak
On March 7, we reported that a massive Dofoil campaign attempted to install malicious cryptocurrency miners on hundreds of thousands of computers. -

Invisible resource thieves: The increasing threat of cryptocurrency miners
The surge in Bitcoin prices has driven widescale interest in cryptocurrencies. -
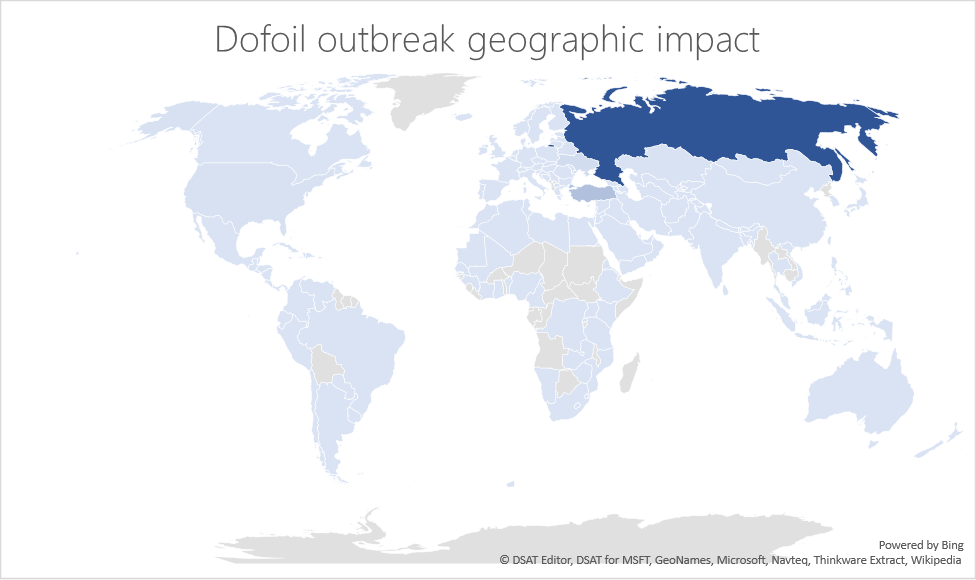
Behavior monitoring combined with machine learning spoils a massive Dofoil coin mining campaign
Update: Further analysis of this campaign points to a poisoned update for a peer-to-peer (P2P) application. -

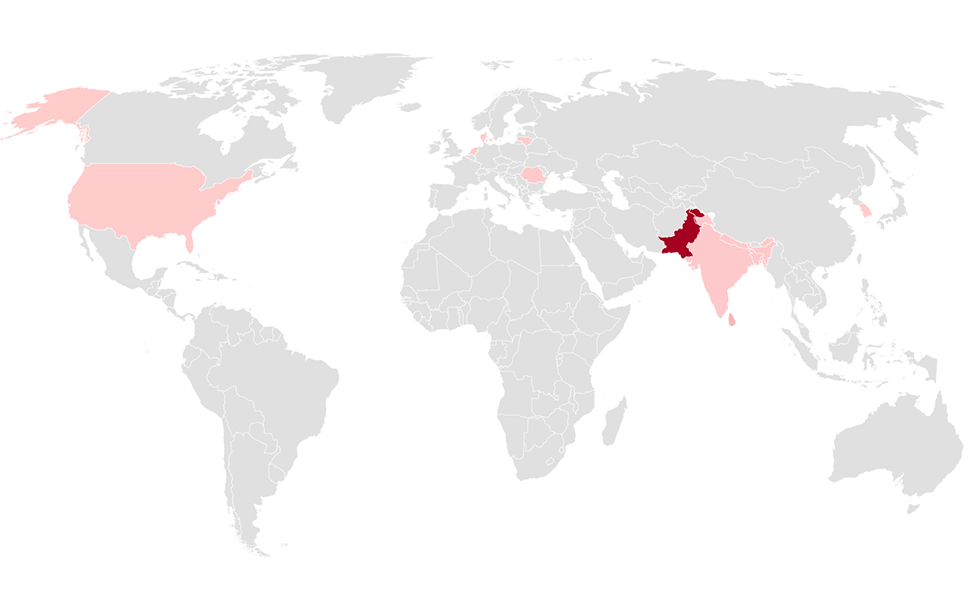
FinFisher exposed: A researcher’s tale of defeating traps, tricks, and complex virtual machines
Office 365 Advanced Threat Protection (Office 365 ATP) blocked many notable zero-day exploits in 2017. -

Protecting customers from being intimidated into making an unnecessary purchase
There has been an increase in free versions of programs that purport to scan computers for various errors, and then use alarming, coercive messages to scare customers into buying a premium version of the same program. -

Now you see me: Exposing fileless malware
Attackers are determined to circumvent security defenses using increasingly sophisticated techniques.





