

Cyberattacker techniques, tools, and infrastructure
Cyberattackers constantly evolve their techniques, tools, and infrastructure to launch increasingly complex attacks. Learn about the latest tactics and how to detect, disrupt, and defend against them.
Refine results
Topic
Products and services
Publish date
-
There are tools available that can ease kick-off activities for CISOs, CIOs, and DPOs.
-
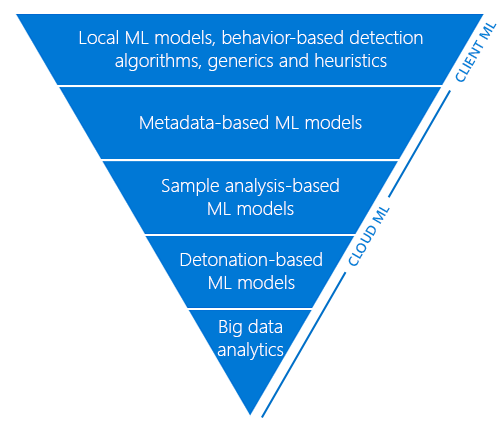
Detonating a bad rabbit: Windows Defender Antivirus and layered machine learning defenses
Windows Defender Antivirus uses a layered approach to protection: tiers of advanced automation and machine learning models evaluate files in order to reach a verdict on suspected malware. -
New tech support scam launches communication or phone call app
(Note: Our Tech support scams FAQ page has the latest info on this type of threat, including scammer tactics, fake error messages, and the latest scammer hotlines. -
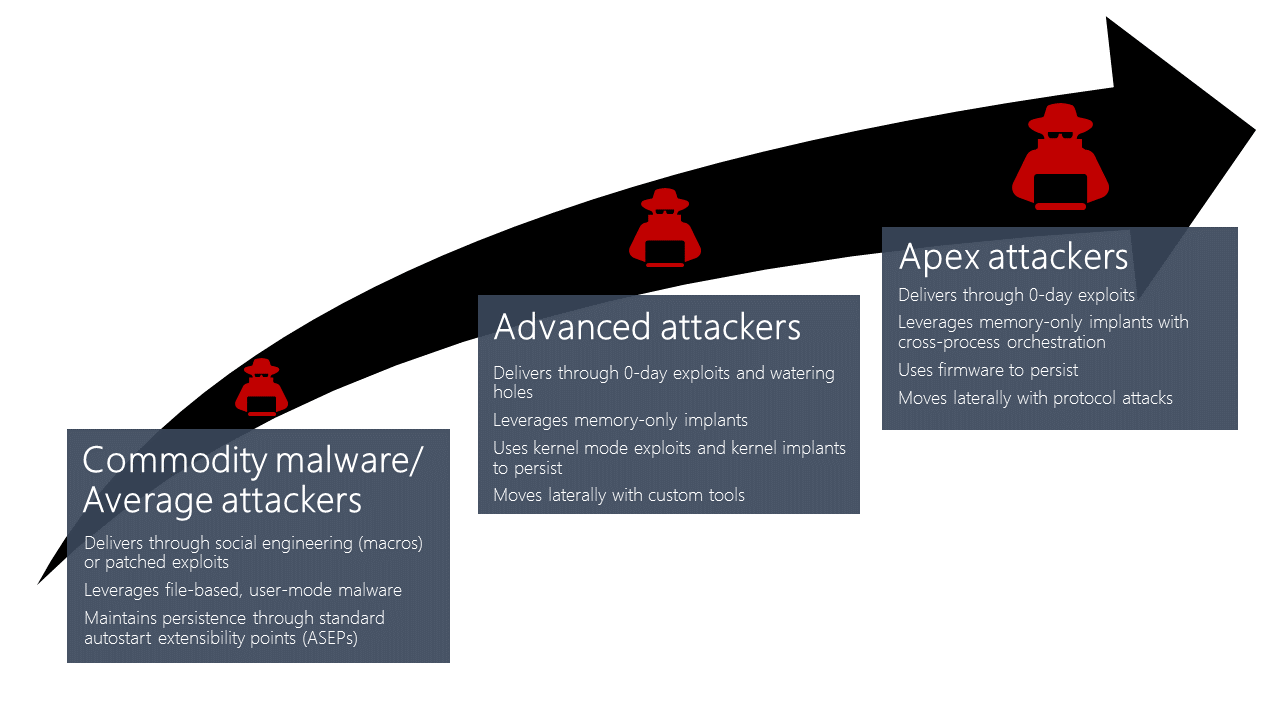
Windows Defender ATP machine learning: Detecting new and unusual breach activity
Microsoft has been investing heavily in next-generation security technologies. -
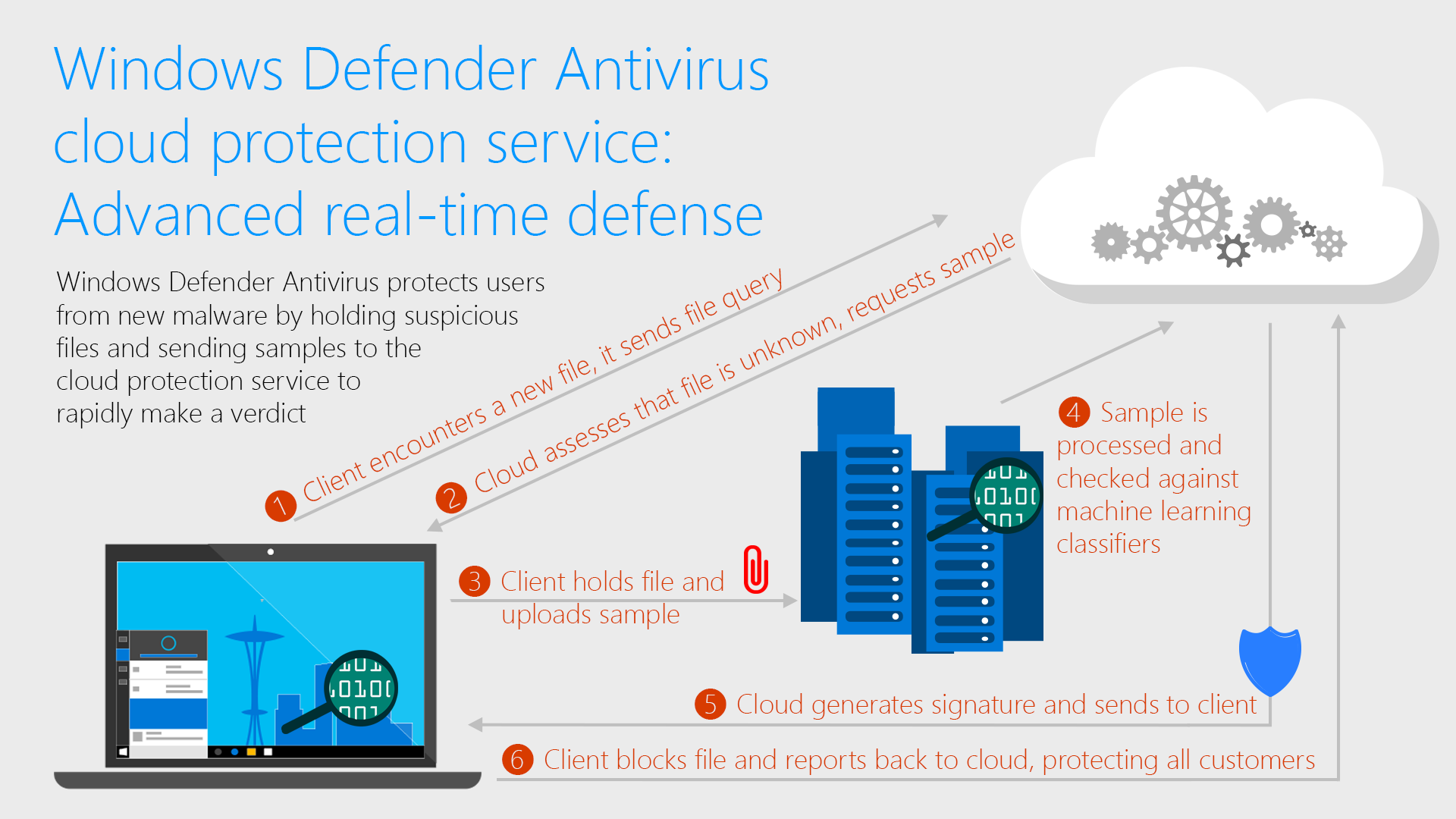
Windows Defender Antivirus cloud protection service: Advanced real-time defense against never-before-seen malware
For cybercriminals, speed is the name of the game. -
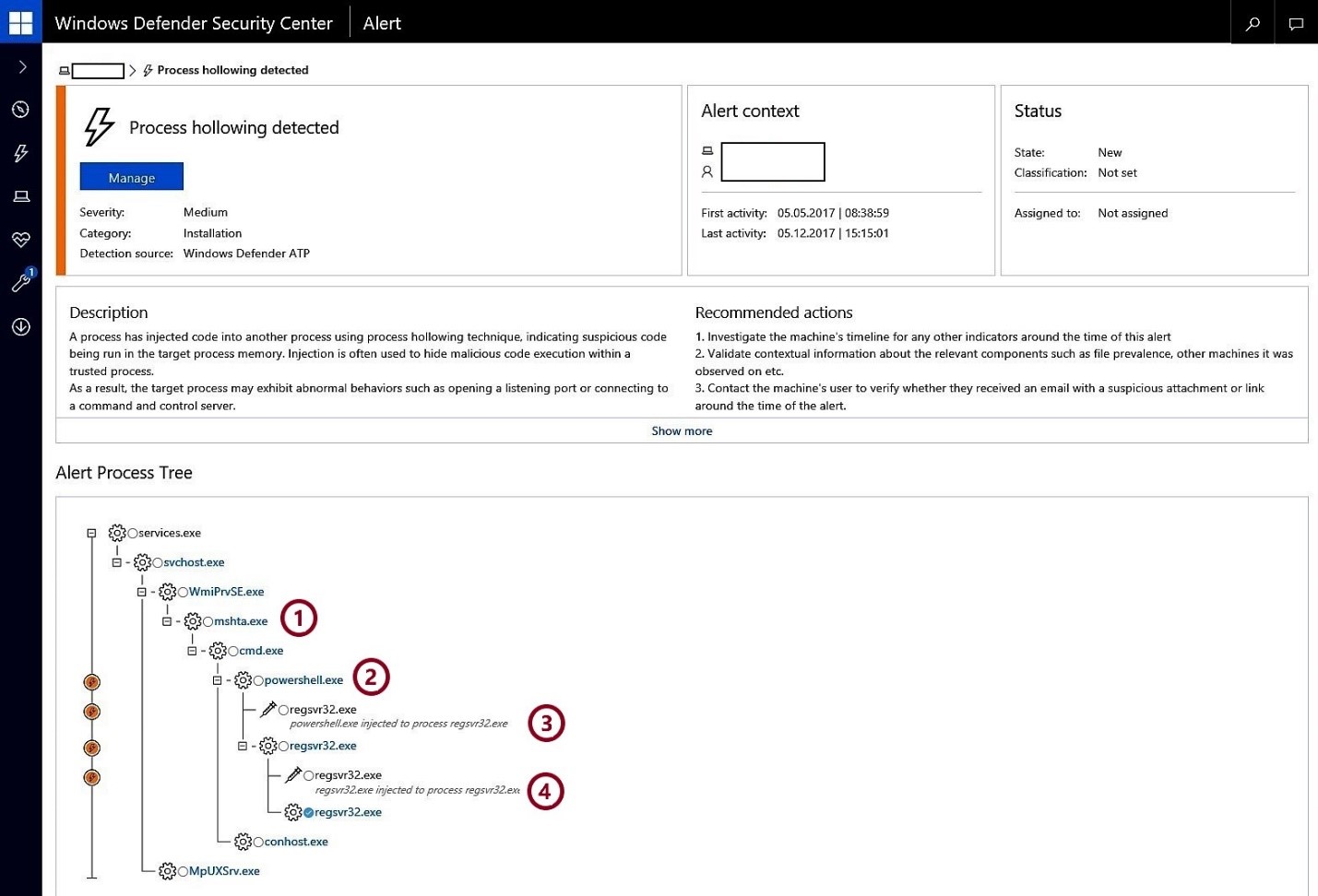
Detecting stealthier cross-process injection techniques with Windows Defender ATP: Process hollowing and atom bombing
Advanced cyberattacks emphasize stealth and persistence: the longer they stay under the radar, the more they can move laterally, exfiltrate data, and cause damage. -
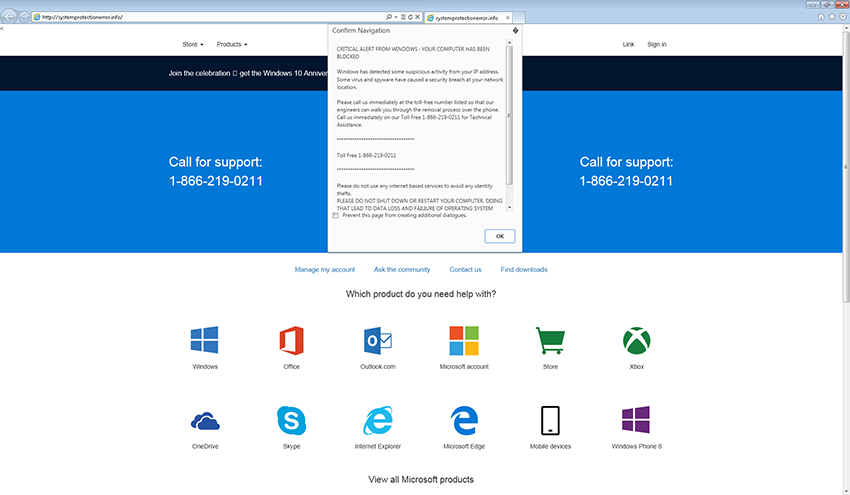
Tech support scams persist with increasingly crafty techniques
Technical support scams continue to evolve, employing more and more complex social engineering tactics that can increase panic and create a false sense of legitimacy or urgency in an effort to get more victims. -
Uncovering cross-process injection with Windows Defender ATP
Windows Defender Advanced Threat Protection (Windows Defender ATP) is a post-breach solution that alerts security operations (SecOps) personnel about hostile activity. -
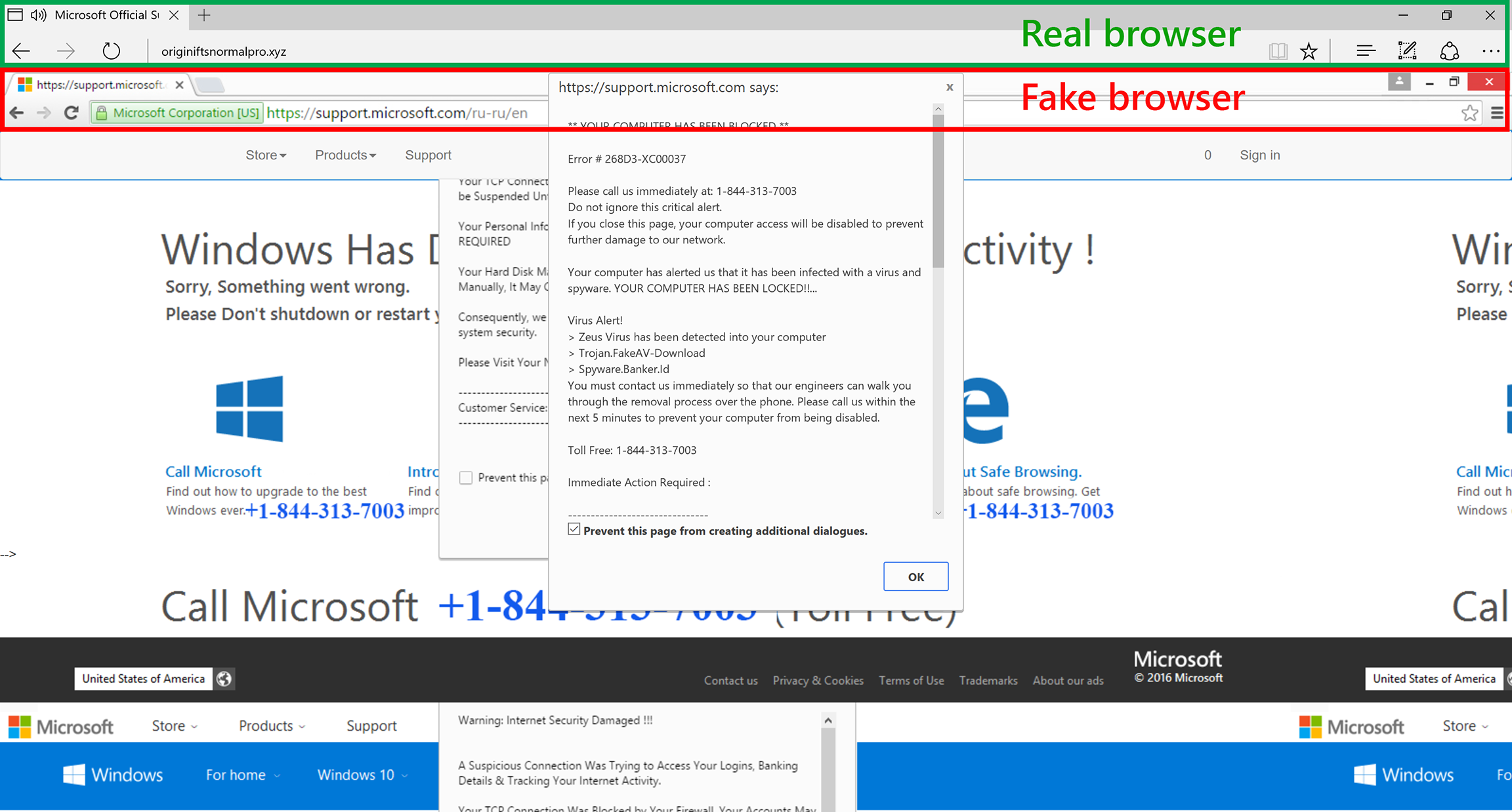
Breaking down a notably sophisticated tech support scam M.O.
The cornerstone of tech support scams is the deception that there is something wrong with your PC. -
Detecting cyber threats
This post is authored by Joe Faulhaber, Senior Consultant ECG In today’s cyber threat landscape, it’s not a question of if an attack will occur, but who will attack and when. -
Twin zero-day attacks: PROMETHIUM and NEODYMIUM target individuals in Europe
Targeted attacks are typically carried out against individuals to obtain intellectual property and other valuable data from target organizations. -

Disrupting the kill chain
This post is authored by Jonathan Trull, Worldwide Executive Cybersecurity Advisor, Enterprise Cybersecurity Group.





