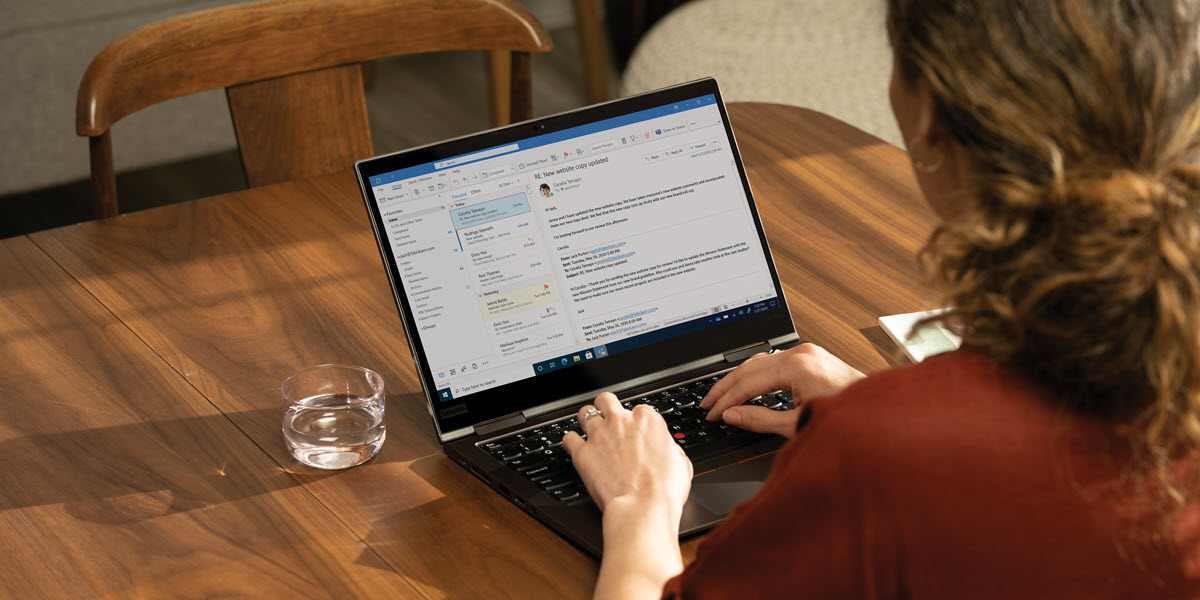


Social engineering and phishing
Social engineering and phishing attacks continue to be the top attack vectors, exploiting human behavior and errors to gain access to sensitive information or advance an attack. Get the latest insights on these threats and how to prevent them.