


Cloud security
Learn more about the solutions, procedures, policies, and controls that help you protect your cloud-based systems and data.
Refine results
Topic
Products and services
Publish date
-
 Learn about the top feature updates for Microsoft Threat Protection in January.
Learn about the top feature updates for Microsoft Threat Protection in January. -

The evolution of Microsoft Threat Protection, December update
Last month, we shared updates on capabilities for securing identities, endpoints, user data, and cloud apps. -
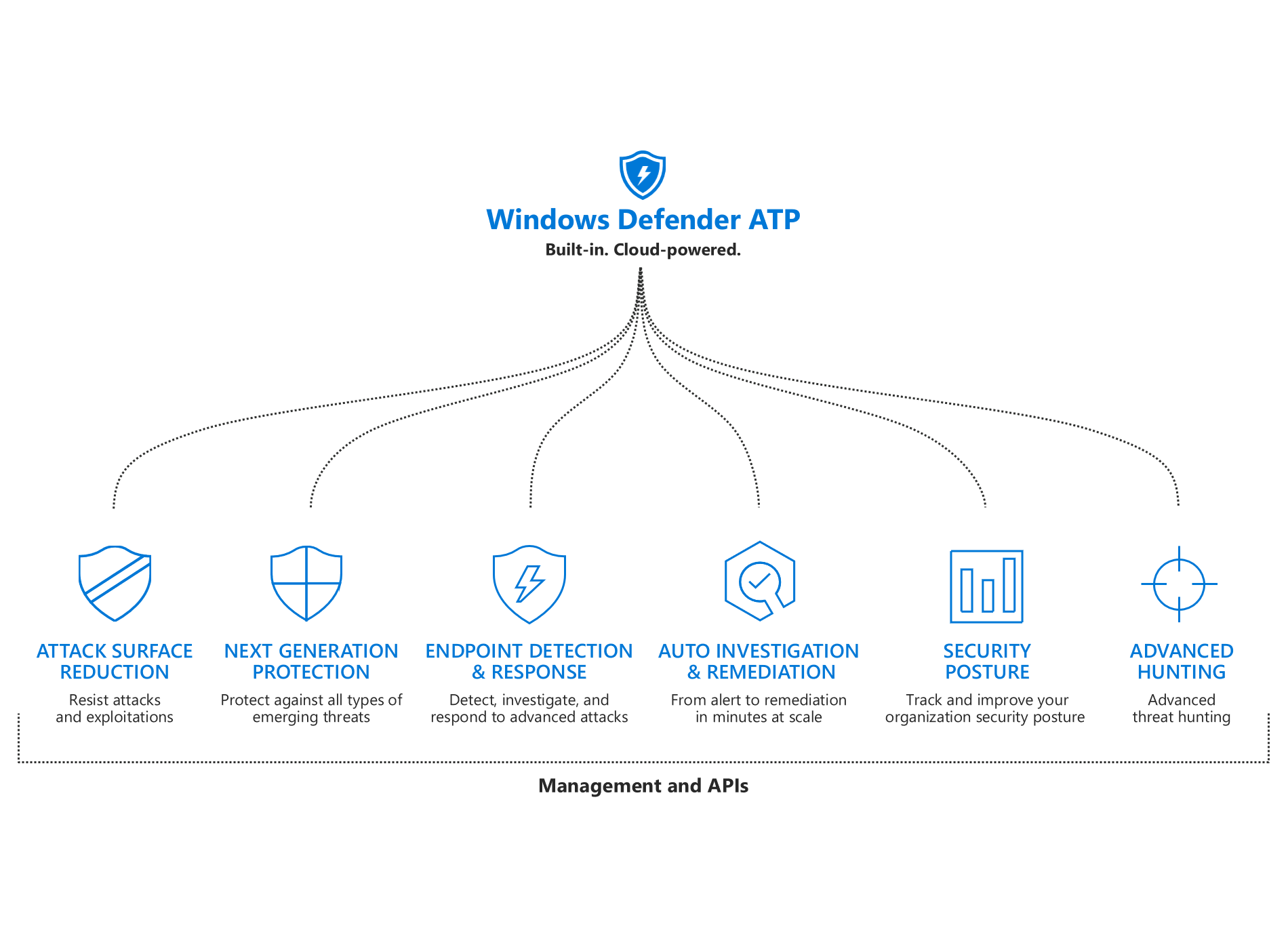
What’s new in Windows Defender ATP
We added new capabilities to each of the pillars of Windows Defender ATP’s unified endpoint protection platform: improved attack surface reduction, better-than-ever next-gen protection, more powerful post-breach detection and response, enhanced automation capabilities, more security insights, and expanded threat hunting. -

The evolution of Microsoft Threat Protection, November update
Learn about the latest enhancements to Microsoft Threat Protection, the premier solution for securing the modern workplace across identities, endpoints, user data, apps, and infrastructure. -
Voice of the Customer: Walmart embraces the cloud with Azure Active Directory
Learn how Walmart embraced the cloud with Azure Active Directory. -
P = NP: Cloud data protection in vulnerable non-production environments
Keeping track of sensitive data is becoming harder as data is being dispersed all over the organization. -
The need and opportunity for adaptive prevention in the cloud
This post is authored by Michael Bargury, Data Scientist, C+E Security. -
From the ground up to the cloud: Microsoft’s Intelligent Security supporting CISOs’ cloud transformation
It’s no secret that Microsoft has embraced the cloud in a big way—from enterprise solutions like Microsoft Azure to Office 365 and Windows. -
Data classification and protection now available for structured data in SQL
This post is authored by Gilad Mittelman, Senior Program Manager, SQL Data Security. -
Securing the modern workplace with Microsoft 365 threat protection – part 4
This post is authored by Debraj Ghosh, Senior Product Marketing Manager, Microsoft 365 Security. -
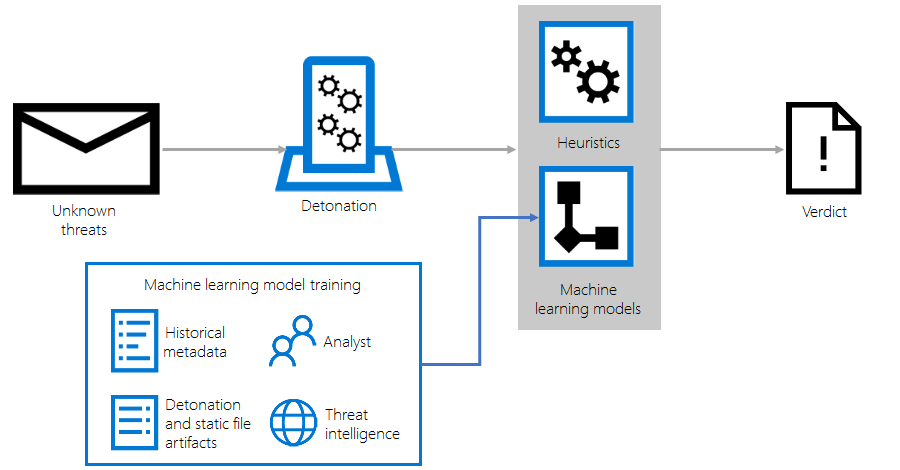
Enhancing Office 365 Advanced Threat Protection with detonation-based heuristics and machine learning
Office 365 Advanced Threat Protection (ATP) uses a comprehensive and multi-layered solution to protect mailboxes, files, online storage, and applications against a wide range of threats. -

Securing the modern workplace with Microsoft 365 threat protection – part 3
This post is authored by Debraj Ghosh, Senior Product Marketing Manager, Microsoft 365 Security.





